What is Cuckoo?¶
Cuckoo is an open source automated malware analysis system.
It’s used to automatically run and analyze files and collect comprehensive analysis results that outline what the malware does while running inside an isolated operating system.
It can retrieve the following type of results:
- Traces of calls performed by all processes spawned by the malware.
- Files being created, deleted and downloaded by the malware during its execution.
- Memory dumps of the malware processes.
- Network traffic trace in PCAP format.
- Screenshots taken during the execution of the malware.
- Full memory dumps of the machines.
Some History¶
Cuckoo Sandbox started as a Google Summer of Code project in 2010 within The Honeynet Project. It was originally designed and developed by Claudio “nex” Guarnieri, who is still the project leader and core developer.
After initial work during the summer 2010, the first beta release was published on Feb. 5th 2011, when Cuckoo was publicly announced and distributed for the first time.
In March 2011, Cuckoo has been selected again as a supported project during Google Summer of Code 2011 with The Honeynet Project, during which Dario Fernandes joined the project and extended its functionality.
On November 2nd 2011 Cuckoo the release of its 0.2 version to the public as the first real stable release. On late November 2011 Alessandro “jekil” Tanasi joined the team expanding Cuckoo’s processing and reporting functionality.
On December 2011 Cuckoo v0.3 gets released and quickly hits release 0.3.2 in early February.
In late January 2012 we opened Malwr.com, a free and public running Cuckoo Sandbox instance provided with a full fledged interface through which people can submit files to be analysed and get results back.
In March 2012 Cuckoo Sandbox wins the first round of the Magnificent7 program organized by Rapid7.
During the Summer of 2012 Jurriaan “skier” Bremer joined the development team, refactoring the Windows analysis component sensibly improving the analysis’ quality.
On 24th July 2012, Cuckoo Sandbox 0.4 is released.
On 20th December 2012, Cuckoo Sandbox 0.5 “To The End Of The World” is released.
On 15th April 2013 we released Cuckoo Sandbox 0.6, shortly after having launched the second version of Malwr.com.
On 1st August 2013 Claudio “nex” Guarnieri, Jurriaan “skier” Bremer and Mark “rep” Schloesser presented Mo’ Malware Mo’ Problems - Cuckoo Sandbox to the rescue at Black Hat Las Vegas.
On 9th January 2014, Cuckoo Sandbox 1.0 is released.
In March 2014 Cuckoo Foundation born as non-profit organization dedicated to growth of Cuckoo Sandbox and the surrounding projects and initiatives.
On 7th April 2014, Cuckoo Sandbox 1.1 is released.
On the 7th of October 2014, Cuckoo Sandbox 1.1.1 is released after a Critical Vulnerability had been disclosed by Robert Michel.
On the 4th of March 2015, Cuckoo Sandbox 1.2 has been released featuring a wide array of improvements regarding the usability of Cuckoo.
During summer 2015 Cuckoo Sandbox started the development of Mac OS X malware analysis as a Google Summer of Code project within The Honeynet Project. Dmitry Rodionov qualified for the project and developed a working analyzer for Mac OS X.
On the 21st of February 2016 version 2.0 Release Candidate 1 is released. This version ships with almost two years of combined effort into making Cuckoo Sandbox a better project for daily usage.
Use Cases¶
Cuckoo is designed to be used both as a standalone application as well as to be integrated in larger frameworks, thanks to its extremely modular design.
It can be used to analyze:
- Generic Windows executables
- DLL files
- PDF documents
- Microsoft Office documents
- URLs and HTML files
- PHP scripts
- CPL files
- Visual Basic (VB) scripts
- ZIP files
- Java JAR
- Python files
- Almost anything else
Thanks to its modularity and powerful scripting capabilities, there’s no limit to what you can achieve with Cuckoo.
For more information on customizing Cuckoo, see the Customization chapter.
Architecture¶
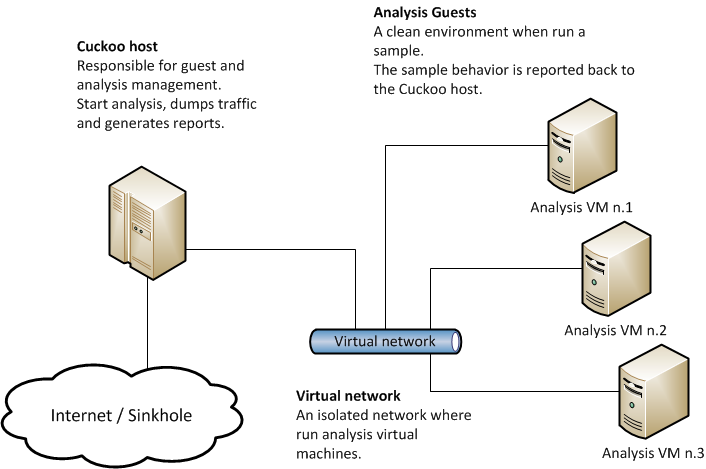
Cuckoo Sandbox consists of a central management software which handles sample execution and analysis.
Each analysis is launched in a fresh and isolated virtual or physical machine. The main components of Cuckoo’s infrastructure are an Host machine (the management software) and a number of Guest machines (virtual or physical machines for analysis).
The Host runs the core component of the sandbox that manages the whole analysis process, while the Guests are the isolated environments where the malware samples get actually safely executed and analyzed.
The following picture explains Cuckoo’s main architecture:
Obtaining Cuckoo¶
Deprecated since version 2.0-rc2: Although Cuckoo can still be downloaded from the website we discourage from doing so, given that simply installing it through pip is the preferred way to get Cuckoo. Please refer to Installing Cuckoo.
Cuckoo can be downloaded from the official website, where the stable and packaged releases are distributed, or can be cloned from our official git repository.
Warning
While being more updated, including new features and bugfixes, the version available in the git repository should be considered an under development stage. Therefore its stability is not guaranteed and it most likely lacks updated documentation.